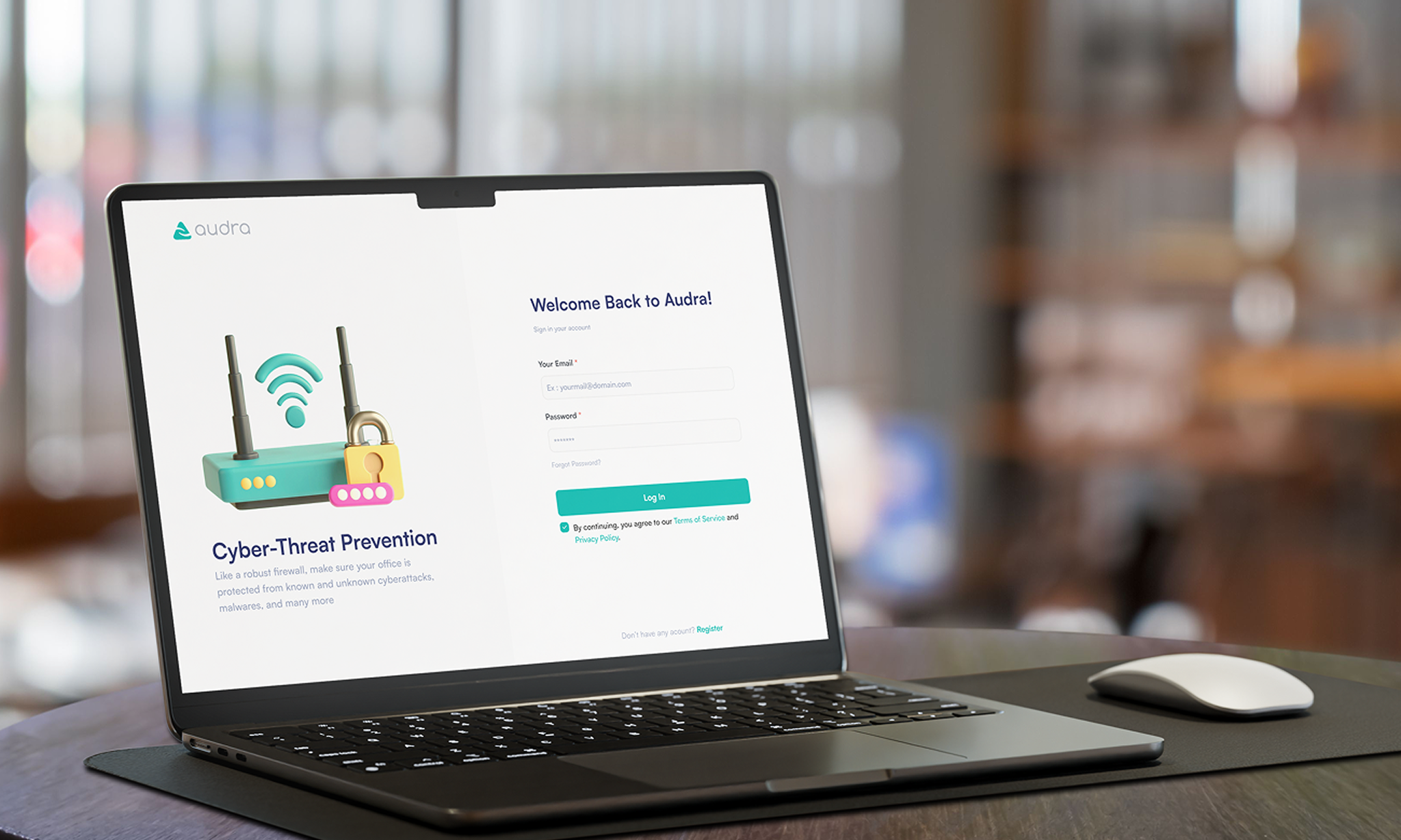
Type: Dashboard (Audra secure, Audra Safe).
Responsibilities: Research, UI, and Design system with team members.
Team Collaboration: Business, Tech, Product, Design team & Project manager
Timeline: 5 weeks
Status: Shipped (Live)
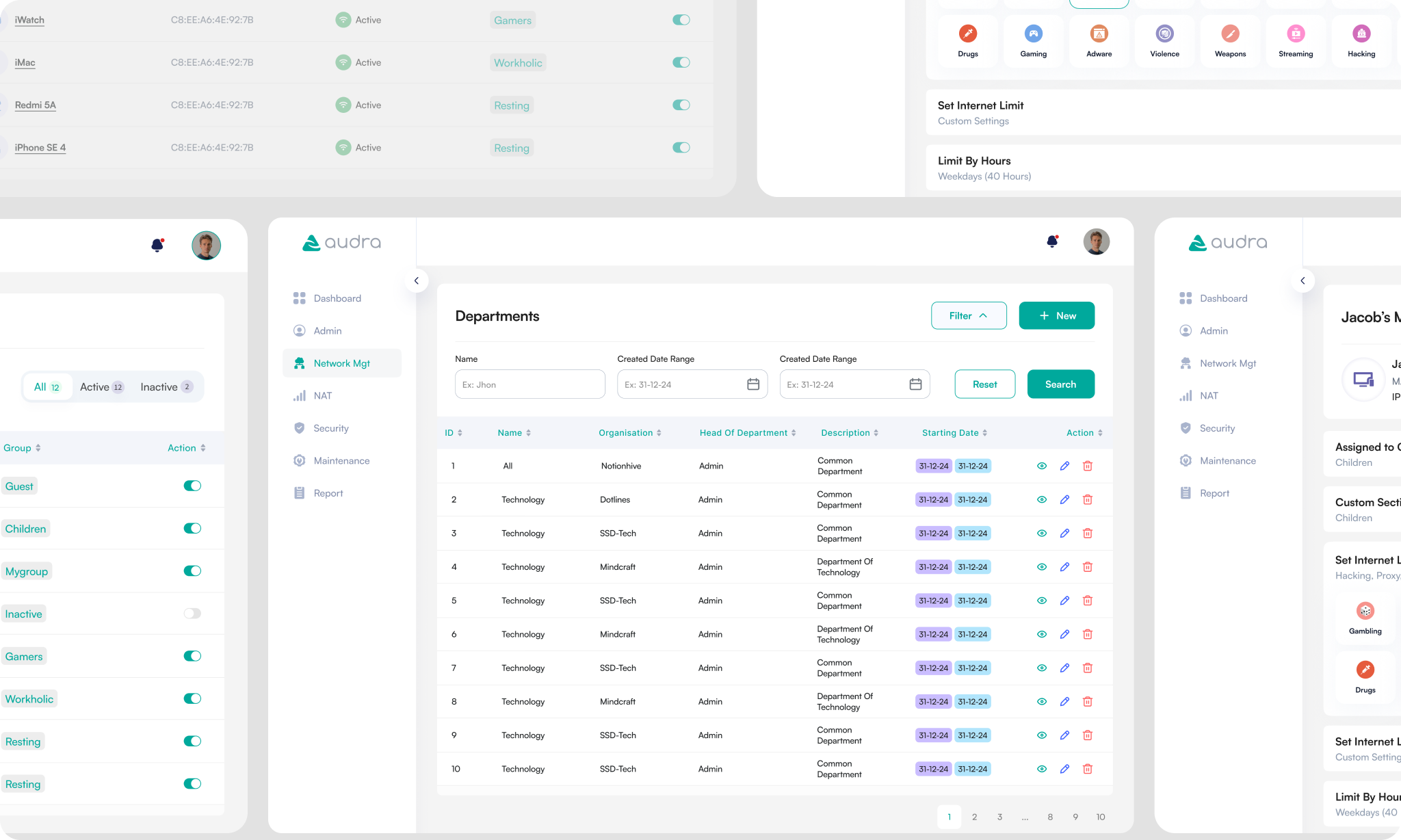
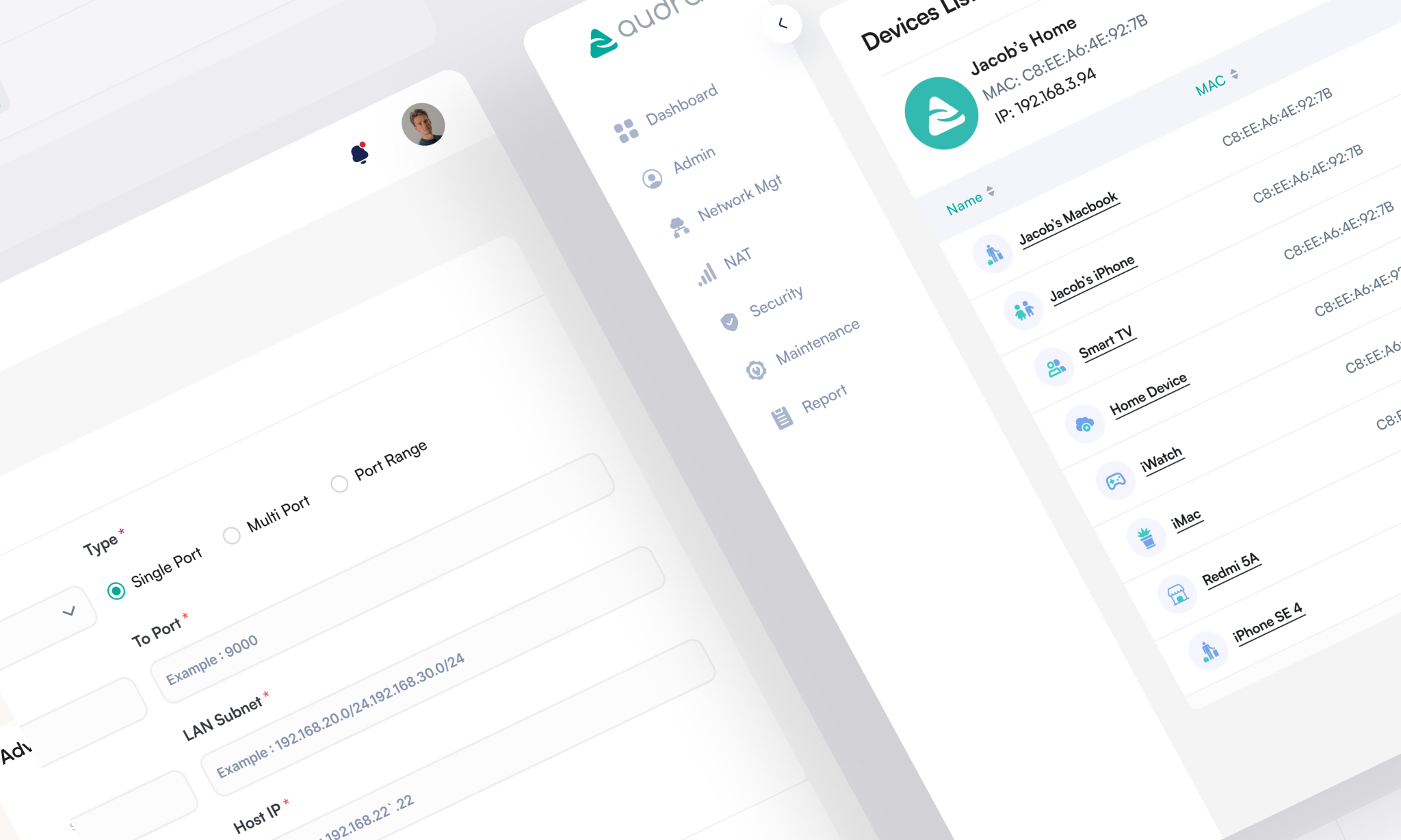
We streamlined multi-tenant management through structured, table-first departmental views. To reduce technical friction, we redesigned advanced networking and security configurations with intuitive, guided forms and binary security toggles and so on. Finally, for home users, we shifted the focus from IP logic to human-centric device management, using visual category-blocking and icon-based scheduling. This unified design system ensures that whether managing an office network or family safety, users experience consistent interaction patterns that maximize control while minimizing configuration errors.
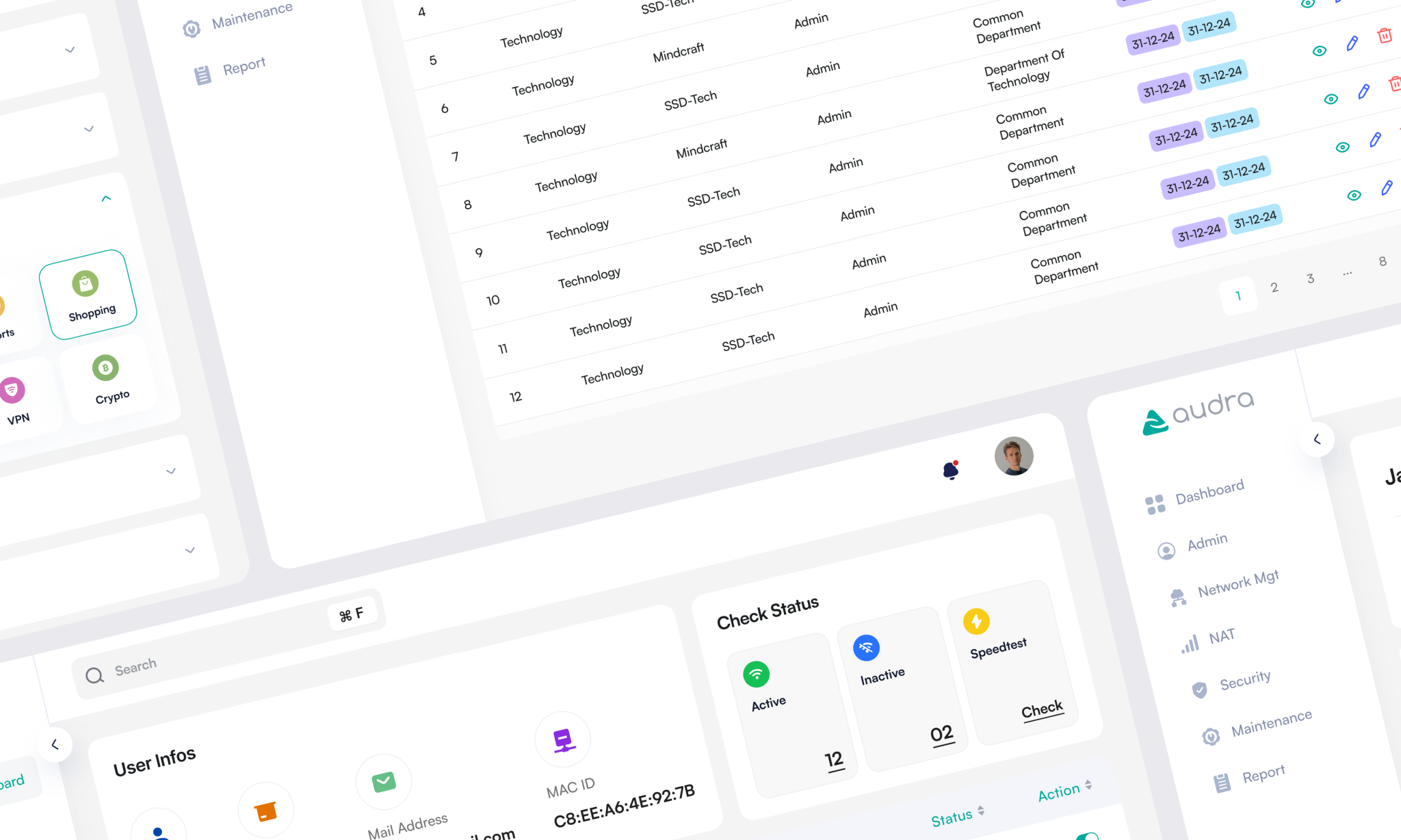
This work helped reduce support tickets by 39% by making troubleshooting and advanced settings clearer and easier to complete correctly, while also improving security feature activation through more approachable controls for protection and device restrictions.